Abstract
The advent of cloud computing has inspired an increasing number of users outsourcing their data to remote servers to enjoy flexible and affordable data management services. However, storing data in a remote cloud server raises data privacy and security concerns, i.e., the integrity and origin of the query results. Although some solutions have been proposed to address these issues, none of them consider the arbitrary dissemination control of authenticated tree-structured data while disseminating to other users.
To address the above concerns, in this paper, we first propose a novel and efficient redactable signature scheme which features editable homomorphic operation and redaction control on tree-structured data. Subsequently, we prove the security properties of our scheme and conduct extensive theoretical and experimental analyses. The experimental results show that our scheme outperforms the existing solutions in disseminating of authenticated tree-structured data with privacy protection and dissemination control in outsourced database (ODB) model.
You have full access to this open access chapter, Download conference paper PDF
Similar content being viewed by others
Keywords
- Outsourced Databases (ODB)
- Redactable Signature Scheme (RSSs)
- Editorial Control
- Monotone Span Programs (MSP)
- Linear Secret Sharing Scheme
These keywords were added by machine and not by the authors. This process is experimental and the keywords may be updated as the learning algorithm improves.
1 Introduction
With the rapid development of cloud computing, it has become prevalent for users and enterprises to lease the computing and storage resources to outsource the storage and management of massive data from local to powerful cloud service provider. Under this new IT Paradigm, database outsourcing [8] is considered as a promising service model by providing a flexible and affordable solution for resource-constrained users to maintain their database services. There exist several real-world cloud service providers such as Amazon Relational Database, Azure, and Enterprise DB which enable users around the world to share and update their outsourced data anytime.
While enjoying all the benefits, the database outsourcing service poses numerous security challenges which influence the overall performance, usability, and scalability. The reason is that a client stores its data at a remote and potentially untrusted database service provider (DSP) rather than a fully controlled local database. What even worse is the outsourced data often contains some sensitive information that cannot be disclosed. Thus privacy of outsourced data is one of the foremost issues in the outsourced database (ODB) model. Moreover, the dishonest DSP may tamper with the data and return an incorrect or incomplete query result for some economic reasons. Hence, another major security requirement in ODB model is the verifiability of the returned results. The verifiability includes (1) the integrity verification of data and (2) that the claimed owner is, in fact, the authorized owner of the data. As a result, for the utilization of the outsourced data, the privacy, integrity, and ownership of the disseminated data should be verified from the users’ perspective.
Redactable signatures [10], a principle solution, can inherently resolve the above issues in ODB model. In the definition of redactable signature schemes (RSSs), parts of a signed document are allowed to be removed by any party without any help from the original signer while preserving the source and integrity verifiability of the remaining subdocument. What’s more, the reserved subdocument and its signature do not reveal any content information about deleted parts. Therefore, RSSs are such a useful primitive that comes in handy in scenarios where only parts of the authenticated data are releasable or required for privacy-preserving, but the origin and integrity authentication of these data must still hold and re-signing is impossible or with striking performance compromise. Nevertheless, the design of RSSs depends on the structure according to which data is organized. Since tree structure is widely used as data organization structure (Extensible Markup Language (XML) is one of today’s most prominent example), the specific design of RSSs for data organized according to tree structure is crucial.
Consider the following application scenario taken from [14]. An XML document describes the health-care record of a person and thus contains sensitive information. Assume that such XML is stored in a remote database server. In order to prevent the sensitive information from being accessed by any unauthorized user, the database manager must be able to prune a tree before disseminating. Still, it should be possible to prove the content and structure integrity of the remaining subtree with respect to the original signer, without having to re-sign the document. Therefore, this can in principle be resolved by RSSs for trees [4].
Related Work. The problem of efficiently verifying the integrity and authenticity of the outsourced tree-structured data at an untrusted server has been explored extensively in the literature. The Merkle Hash Tree (MHT) [19] is the most widely used authentication technique for trees and has been exploited for the data dissemination [9, 26]. The main problem of this technique is that authentication process does not preserve the confidentiality (hiding) of sensitive information. Therefore, MHT is vulnerable to inference attacks. The searchable encryption schemes [6, 28] have been proposed to protect the privacy of the outsourced data. However, these technologies can not ensure the integrity and authenticity of the outsourced data.
Disseminating parts of a document while maintaining the integrity and authenticity of the remaining data is an issue that has been approached. Kundu and Bertino [14] proposed a signature scheme for trees, which assures both confidentiality and integrity efficiently. However, their scheme falls short of providing formal security definitions and proofs. To solve this issue, Brzuska et al. [4] gave rigorous security definitions for redactable signatures for trees, and gave a construction that can be proven secure under standard cryptographic assumptions. However, they did not consider the case when the structure is not separated from content which results in an attack on their proposed scheme. Samelin et al. [22] presented a provably secure RSS for trees which not only supports to redact structure and content independently but also controls consecutive redaction. On top of that, Samelin et al. [23] presented a new attack on the RSS introduced by Kundu and Bertino [14], which is an extension of the works done by Brzuska et al. [4] and Samelin et al. [22]. The secure model is more flexible than the one introduced by Kundu and Bertino [14]. Kundu et al. proposed leakage-free RSSs for trees [12, 13] based on secure naming scheme, which is applicable in enabling secure data management in the emerging ODB model as well as in healthcare systems [27].
Motivation. In the definition of conventional RSSs for trees, anyone who possesses the tree-signature pair can execute redaction operation publicly. However, current RSSs for trees are facing with the threat from dishonest redactor or additional redaction because the signature holder can modify the signed trees unrestrictedly. Since the content of each node in a tree can be organized or disseminated in distinct manners, and releasing arbitrary subtrees often makes no sense. Therefore, redaction control is crucial for signers to authorize redactable nodes of authenticated trees. It provides a feasible mechanism for signers to prevent the arbitrary redaction operation of a signed tree from dishonest signature holders, especially in the ODB model where the DSP is untrusted.
In the previous work, Steinfeld et al. [25] introduced CEAS with which signers can specify which portions of the authenticated document is redactable. Afterward, Bull et al. [5] introduced a new hierarchical redaction control policy whose encoding is dramatically smaller. Miyazaki et al. [21] proposed the first authenticated document sanitizing scheme with redaction condition control. However, the signature length of this scheme is relatively long, and the redaction condition reveals the number of sanitized portions. In order to resolve these problems, Miyazaki et al. [20] proposed another authenticated document sanitizing scheme based on bilinear maps. Recently, Ma et al. [16, 17] also presented the secure and efficient design of RSSs with subdocument redaction control. At present, although there exist a number of related works that have brought in different methods to prevent unauthorized redaction manipulation, none of them consider the redaction control mechanism in RSSs for trees.
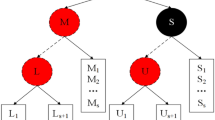
Contributions. To satisfy the aforementioned requirements, in this work, we propose an efficient redactable signature scheme for trees with fine-grained redaction control (RSS-TFRC) which supports the integrity and origin verification of the tree-structured data returned from DSP with privacy preserving and dissemination control. The framework of applying RSS-TFRC in ODB model is described as follows. The data owner generates a redactable signature for a tree and uploads the tree-signature pair to database servers. Since the redactable signature is embedded with a redaction control policy by the data owner, any unauthorized redaction manipulation from attackers or DSP is prohibited. Thus, when data users want to access the data stored on database servers, DSP generates the corresponding redacted tree-signature pair and sends them to users. After receiving the subtree, queries can verify its integrity and origin without obtaining any information of the pruned nodes in the original tree. The main contributions in this paper can be summarized as follows:
-
We for the first time propose a practical RSS-TFRC. Our design supports the integrity and origin verification of the released tree-structured data from DSP without revealing any sensitive information.
-
We formally define the proposed RSS-TFRC and its security properties in terms of unforgeability, privacy, and transparency. The security properties are proved in a reduction mode.
-
We evaluate the performance of our scheme through theoretical comparison and practical implementation, which further validates that the proposed RSS-TFRC is indeed an efficient integrity and origin verification solution for tree-structured data dissemination in ODB model.
Organization of This Paper. The rest of this paper is organized as follows. Section 2 is devoted to the introduction of several cryptographic primitives used in this paper. The definitions of RSS-TFRC and its security properties are described in Sect. 3. Section 4 details our concrete construction of RSS-TFRC and its correctness analysis. We analyze the performance and prove the security of our scheme in Sect. 5. Finally, Sect. 6 concludes this paper.
2 Preliminaries
This section defines the general notations used in the paper, followed by a review of document abstraction, access structure, monotone span program, and linear secret sharing scheme. Finally, the bilinear aggregate signature is introduced.
2.1 General Notations
Let \( s \overset{R}{\leftarrow } S\) denote the assignment of a uniformly and independently distributed random element from the set S to the variable s. The symbol \(\perp \notin \{0,1\}^{*}\) denotes an error or an exception. We use the notation \(\mathrm {Adv}^{\textsf {Event}}_{\textsf {exp}}(\lambda )\) to denote the probability of event \(\textsf {Event}\) in experiment \(\textsf {exp}\). An integer \(\lambda \in \mathbb {N}\) is the security parameter, which allows controlling the security degree of a scheme by controlling the length of the secret key. We say that a scheme achieves the security notion if the success probability for all efficient PPT (probabilistic polynomial time) attackers in breaking the scheme is a negligible function of \(\lambda \) (a function \(\epsilon (\lambda )\) is called negligible if for each \(\jmath > 0\), there exists \({\lambda }_0\) such that \(\epsilon (\lambda ) < \frac{1}{{\lambda }^{\jmath }}\) for all \(\lambda > {\lambda }_0\)).
2.2 Document Abstraction
Trees. A tree [4] is a connected graph \(\varUpsilon (V, E)\) which consists of a nonempty finite set V of vertices, a set E of edges and does not contain cycles. The edge between nodes a and b is denoted \(l(a,b) \in V \times V\). A node a represents an atomic unit of data, which is always shared as a whole or is not shared at all. A tree \(\varUpsilon _r\) is rooted if one vertex \(r \in V\) (the root) is distinguished from the others. If \(l(a_i, b_i)\) is an edge, then the node that is closer to r is called the parent of the other node, while the latter is called a child of the former. If two vertices have the same parent, then these two vertices are called siblings. The vertex with no children is called leaf. The root is the only node without parents. A tree is called ordered tree if there is a special order among the children of each vertex. For any vertex a, the content of this node is referred to as \(c_a\). A subtree of tree \(\varUpsilon (V, E)\) is denoted by \(\varUpsilon _\delta (V_\delta , E_\delta )\), where \(V_\delta \subseteq V\) and \(E_\delta \subseteq E\).
Secure Names. As we consider ordered trees, we also have to protect the order of siblings of a node; we do this by assigning a secure name to each node in a tree. The secure naming schemes introduced by Kundu et al. in [12, 13] can be used for the purpose of verifying the order between any pair of nodes in a tree without leaking any information of other nodes and their relationship (e.g., whether they are adjacent siblings, how many other siblings are between them, etc.). Their approach follows a bottom-up strategy. Please refer to [12, 13] for the definition, concrete construction and security proof of secure naming scheme.
2.3 Access Structure
Definition 1
(Access Structure [1]). Let \(\mathcal {U}\) be a set of parties. An access structure on \(\mathcal {U}\) is a collection \(\mathbb {A}\) of non-empty sets of parties, i.e., \(\mathbb {A} \subseteq 2^{\mathcal {U}} \backslash \{\emptyset \}\). The sets in \(\mathbb {A}\) are called the authorized sets and the sets not in \(\mathbb {A}\) are called unauthorized sets with respect to \(\mathbb {A}\). An access structure \(\mathbb {A}\) is called monotone access structure if \(\forall B, C \in \mathbb {A}\) : if \(B\in \mathbb {A}\) and \(B \subseteq C\), then \(C \in \mathbb {A}\). A set B satisfies \(\mathbb {A}\) (in other words, \(\mathbb {A}\) accept B) if and only if B is an authorized set in \(\mathbb {A}\), i.e., \(B \in \mathbb {A}\).
In the context of this paper, the role of parties is played by tree node. Thus, the access structure \(\mathbb {A}\) contains the authorized subsets of nodes that are not redactable. We restrict our attention to monotone access structure.
2.4 Monotone Span Program
Monotone span program (MSP), a linear algebraic model of computation, constitutes a significant component in realizing our fine-grained redaction control policy. The fine-grained redaction control policy of our construction is depicted by a monotone boolean formula in the first stage, which is the combination of some nodes that are allowed to be disclosed in a tree. We will use monotone span program to represent the monotone boolean formula. In order to represent the monotone boolean formula using monotone span program, we should first convert the monotone boolean formula into an access tree with the method introduced in [7]. The tree here we use is a binary tree: every interior node is either AND or OR gate and each leaf node corresponds to message blocks. An access tree can be converted into an equivalent matrix \(\mathbf {E}\) with the technique in [15]. Refer to [7, 15] for more details about the construction and operating principle of MSP.
2.5 Linear Secret Sharing Scheme
Definition 2
(Linear Secret-Sharing Scheme (LSSS) [1]). A secret-sharing scheme \(\varPi _\mathbb {A}\) for the access structure \(\mathbb {A}\) over a set \(\mathcal {S}\) is called linear (over \(\mathbb {Z}_p\)) if
-
The shares of a secret \(s \in \mathbb {Z}_{p}\) for each party form a vector over \(\mathbb {Z}_p\).
-
For each access structure \(\mathbb {A}\) on \(\mathcal {S}\), there exists a matrix \(\mathbf {E}\) with n rows and c columns called the sharing-generating matrix for \(\varPi \). A function \(\rho \) defines each row number i of matrix \(\mathbf {E}\) as \(\rho (i)\), that labels the rows of \(\mathbf {E}\) with elements from \(\mathcal {S}\). Let vector \(\mathbf {\omega } = (s, y_{2}, \ldots , y_{c})^{T}\), where s is the secret will be shared into n parts, and \(y_{2}, \ldots , y_{c}\) are chosen in \(\mathbb {Z}_{p}\) randomly. \(\mathbf {E}\mathbf {\omega }\) is the vector of n shares of s according to \(\varPi \) and each share in \(\mathbf {E}\mathbf {\omega }\) “belongs” to the party \(\rho (i)\). We refer to the pair \((\mathbf {E}, \rho )\) as the policy of the access structure \(\mathbb {A}\).
The existence of an efficient LSSS for tree access structure is equivalent to the existence of a small MSP for the monotone boolean formula of that access structure [1, 11]. LSSS enjoys the linear reconstruction property and security requirement. Let \(A \in \mathbb {A}\) be an authorized set for the access structure \(\mathbb {A}\) encoded by the policy \((\mathbf {E}, \rho )\) and define \(I \subset \{ 1, 2, \ldots , n \}\) as \(I = \{ i : \rho (i) \in A\}\). The reconstruction requirement asserts that the vector \((1, 0, \ldots , 0)\) is in the span of rows of \(\mathbf {E}\) indexed by I. Then, there exist constants \(\{\omega _{i} \in \mathbb {Z}_{p}\}_{i \in I}\) such that, if \(\{\lambda _{i} = (\mathbf {E}\mathbf {\omega })_{i}\}_{i \in I}\) are valid shares of a secret s according to \(\varPi \) then \(s = \sum _{i \in I} \omega _{i}\lambda _{i}\).
2.6 Bilinear Aggregate Signature
The first bilinear aggregate signature, introduced by Boneh et al. in [2] (hereafter referred to as the BGLS scheme), is constructed from the short signature scheme based on bilinear maps due to [3]. The basic idea is aggregating signatures generated by different signers on distinct message into one short signature based on elliptic curves and bilinear mappings. The result of this aggregation is an aggregate signature \(\sigma \) whose length is the same as that of any individual signatures. Their scheme is based on Gap Diffie-Hellman groups (GDH) [3] where the Computational Diffie-Hellman (CDH) problem is hard while the Decisional Diffie-Hellman (DDH) problem is easy. Refer to [2, 3] for more details about the construction of BGLS scheme and Gap Diffie-Hellman problem.
3 Definitions of RSS-TFRC
The formal scheme and security definitions of RSSs for trees have already been identified by Brzuska et al. in [4]. To prevent arbitrary redaction operations of an authenticated tree from any party in a fine-grained manner, we extend their definitions and first formally define RSS-TFRC. In this section, we will formally define the RSS-TFRC and its security properties via unforgeability, privacy, and transparency.
3.1 The Scheme Definition of RSS-TFRC
In the following, a message is represented by a tree \(\varUpsilon (V,E)\) which consists of a number of structured message blocks. \(\mathcal {P}\) is associated with the encoding of some subtrees of \(\varUpsilon (V,E)\), which can be used by signer to specify those subsets that the third party is not allowed to redact. The design of \(\mathcal {P}\) is specified according to concrete applications. \(\varUpsilon _{\delta '}(V_{\delta '},E_{\delta '})\) is used to describe the subtree a redactor intend to redact. \(\varUpsilon _\delta (V_\delta ,E_\delta )\) is the subtree after removing subtree \(\varUpsilon _{\delta '}(V_{\delta '},E_{\delta '})\) from \(\varUpsilon (V,E)\) \((\varUpsilon _\delta (V_\delta ,E_\delta ) \leftarrow \varUpsilon (V,E) \backslash \varUpsilon _{\delta '}(V_{\delta '},E_{\delta '}))\). \(\mathcal {P}(\varUpsilon _\delta (V_\delta ,E_\delta )) =1\) means that \(\varUpsilon _{\delta '}(V_{\delta '},E_{\delta '})\) is a valid redaction description with respect to \(\mathcal {P}\) and \(\varUpsilon (V,E)\), which further indicates that \(\varUpsilon _\delta (V_\delta ,E_\delta )\) satisfies \(\mathcal {P}\).
Definition 3
An RSS-TFRC consists of four polynomial time algorithms (KeyGen, Sign, Verify, Redact) such that:
\(\mathsf{KeyGen}(1^{\lambda })\): This probabilistic algorithm takes as input a security parameter \(1^\lambda \) and outputs a public key pk for verification and a secret key sk for signing: \((pk, sk) \leftarrow \mathsf{KeyGen}(1^{\lambda })\).
\(\mathsf{Sign}(sk, \varUpsilon (V,E), \mathcal {P})\): This algorithm takes as input a secrete key sk, a tree \(\varUpsilon (V,E)\), and a fine-grained redaction control policy \(\mathcal {P}\). It outputs a tree-signature pair \((\varUpsilon (V,E), \sigma _\varUpsilon )\): \( (\varUpsilon (V,E), \sigma _\varUpsilon ) \leftarrow \mathsf{Sign}(sk, \varUpsilon (V,E), \mathcal {P})\). In the simplest case, \(\mathcal {P}\) is part of the signature \(\sigma _\varUpsilon \) and always be recoverable by the third party.
\(\mathsf{Verify}(pk, \varUpsilon (V,E), \sigma _\varUpsilon )\): This algorithm takes as input a public key pk, a tree \(\varUpsilon (V,E)\), and a signature \(\sigma _\varUpsilon \). It outputs a decision \(b\in \{{1, 0}\}\) verifying that \(\sigma _\varUpsilon \) is a valid redactable signature on a tree \(\varUpsilon (V,E)\) with respect to a public key pk: \(b \leftarrow \mathsf{Verify}(pk, \varUpsilon (V,E), \sigma _\varUpsilon )\).
\(\mathsf{Redact}(pk, \sigma _\varUpsilon , \varUpsilon (V,E), \varUpsilon _{\delta '}(V_{\delta '},E_{\delta '}))\): This algorithm takes as input the public key pk of the signer, a valid signature \(\sigma _\varUpsilon \), an original authenticated tree \(\varUpsilon (V,E)\), and a redaction subtree \(\varUpsilon _{\delta '}(V_{\delta '},E_{\delta '})\). Before the redaction manipulation, it will check if \(\sigma _\varUpsilon \) is a valid redactable signature on a tree \(\varUpsilon (V,E)\) with respect to a public key pk, \(V_{\delta '} \subseteq V\), and \(E_{\delta '} \subseteq E\). Once the inputs satisfy these requirements, the third party cut the subtree \(\varUpsilon _{\delta '}(V_{\delta '},E_{\delta '})\) from \(\varUpsilon (V,E)\) and updates the signature \(\sigma _\varUpsilon \). Then, it outputs the updated signature \(\sigma _{\varUpsilon _\delta }\) for the pruned tree \(\varUpsilon _\delta (V_\delta ,E_\delta ) \leftarrow \varUpsilon (V,E) \backslash \varUpsilon _{\delta '}(V_{\delta '},E_{\delta '})\) (or \(\bot \), indicating an error), where \(V_\delta = V_\delta \backslash V_{\delta '}\) and \(E_\delta = E_\delta \backslash E_{\delta '}\): \((\varUpsilon _\delta (V_\delta ,E_\delta ), \sigma _{\varUpsilon _\delta }) \leftarrow \mathsf{Redact}(pk, \varUpsilon _{\delta '}(V_{\delta '},E_{\delta '}), \varUpsilon (V,E), \sigma _\varUpsilon )\).
3.2 Correctness of RSS-TFRC
In general, the correctness property of an RSS-TFRC requires that every genuinely generated signature is verified valid by Verify algorithm.
Definition 4
\(\mathbf {(Signing\,Correctness).}\) For any tree \(\varUpsilon (V,E)\), any security parameter \(\lambda \), any key pair \((pk, sk) \leftarrow \mathsf{KeyGen}(1^{\lambda })\), any fine-grained redaction control policy \(\mathcal {P}\), and any signature \((\varUpsilon (V,E), \sigma _\varUpsilon ) \leftarrow \mathsf{Sign}(sk, \varUpsilon (V,E), \mathcal {P})\), we have \(\mathsf{Verify}(pk, \varUpsilon (V,E), \sigma _\varUpsilon ) = 1\).
Definition 5
\(\mathbf {(Redaction\,Correctness).}\) For any signature \((\varUpsilon (V,E), \sigma _\varUpsilon ) \leftarrow \mathsf{Sign}(sk, \varUpsilon (V,E), \mathcal {P})\) satisfies \(\mathsf{Verify}(pk, \varUpsilon (V,E), \sigma _\varUpsilon ) = 1\), any subtree \(\varUpsilon _{\delta '}(V_{\delta '},E_{\delta '})\), any subset of vertices \(V_{\delta '} \subseteq V\), any subset of edges \(E_{\delta '} \subseteq E\) such that \(V_\delta = V_\delta \backslash V_{\delta '}\) and \(E_\delta = E_\delta \backslash E_{\delta '}\), and any \( (\varUpsilon _\delta (V_\delta ,E_\delta ), \sigma _{\varUpsilon _\delta }) \leftarrow \mathsf{Redact}(pk, \varUpsilon _{\delta '}(V_{\delta '},E_{\delta '}), \varUpsilon (V,E), \sigma _\varUpsilon )\) such that \(\mathcal {P}(\varUpsilon _\delta (V_\delta ,E_\delta )) =1\), we have \(\mathsf{Verify}(pk, \varUpsilon _\delta (V_\delta ,E_\delta ), \sigma _{\varUpsilon _\delta }) = 1\).
3.3 Unforgeability of RSS-TFRC
The unforgeability definition of RSS-TFRC is defined analogously to the standard unforgeability definition of conventional digital signature schemes. Informally, it requires that even if signatures on different trees are available by adaptive signature queries, no one should be able to compute a valid signature on a tree \(\varUpsilon ^*\) without having access to the secret key sk provided that \(\varUpsilon ^*\) is neither (A) a subtree of any tree queried to the signing oracle (i.e., \(\varUpsilon ^* \nsubseteq \varUpsilon _i\)), or (B) is a subtree of a tree \(\varUpsilon _i\) queried to the signing oracle, but does not satisfy the fine-grained redaction control policy \(\mathcal {P}_i\) (i.e., \(\varUpsilon ^* \subsetneq \varUpsilon _i\) and \(\mathcal {P}_i(\varUpsilon ^*) \ne 1\)).
Definition 6
\(\mathbf {(Unforgeability).}\) An \(\textsf {RSS}\hbox {-}\textsf {TFRC}:=(\mathsf{KeyGen,}\ \mathsf{Sign,}\ \mathsf{Verify,} \mathsf{Redact})\) is EUF-CTA (existentially unforgeable under adaptive chosen-tree attacks) if the probability of any PPT adversary \(\mathcal {A}\) in winning the following game is a negligible function of the security parameter \(\lambda \).
\(\mathbf {Game\,1:}\) Unforgeability \(_{\mathcal {A}}^{\textsf {RSS}\hbox {-}\textsf {TFRC}}\)
-
Setup: The challenger runs \(\mathsf{KeyGen}\) to obtain a public key pk and a private key sk. The adversary \(\mathcal {A}\) is given pk.
-
Query Phase: Proceeding adaptively, \(\mathcal {A}\) requests signatures with pk on at most \(q_S\) trees of his choice \(\varUpsilon _1, \varUpsilon _2, \cdots , \varUpsilon _{q_S}\). For each query, the challenger runs \((\varUpsilon _i, \sigma _{\varUpsilon _i}) \leftarrow \textsf {Sign}(sk, \varUpsilon _i, \mathcal {P}_i)\) and forwards \((\varUpsilon _i, \sigma _{\varUpsilon _i})\) to \(\mathcal {A}\). Note that \(\mathcal {A}\) is also allowed to choose \(\mathcal {P}_i\).
-
Output: Eventually, \(\mathcal {A}\) outputs a pair \((\varUpsilon ^*, \sigma _{\varUpsilon ^*})\) and wins the above game if (1) \(\textsf {Verify}(pk, \varUpsilon ^*, \sigma _{\varUpsilon ^*})= 1\) and (2) for all \(i=1, 2, \ldots , q_S\) we have either \(\varUpsilon ^* \nsubseteq \varUpsilon _i\) or \(\varUpsilon ^* \subsetneq \varUpsilon _i\) but \(\mathcal {P}_i(\varUpsilon ^*) \ne 1\).
3.4 Privacy of RSS-TFRC
The privacy requirement of RSS-TFRC is to guarantee the confidentiality of the nodes of the tree that were pruned. This is formalized by demanding that, given a subtree with a signature and two possible source trees, it is infeasible for one to decide from which source tree the subtree stems from. The privacy definition for RSS-TFRC is based on the indistinguishability game for encryption schemes: an adversary \(\mathcal {A}\) chooses two pairs of trees and subtrees \((\varUpsilon _0, \varUpsilon _{\delta '_0})\), \((\varUpsilon _1, \varUpsilon _{\delta '_1})\) such that \(\varUpsilon _0 \backslash \varUpsilon _{\delta '_0} = \varUpsilon _1 \backslash \varUpsilon _{\delta '_1}\), i.e., removing the subtrees results in isomorphic trees. Furthermore, \(\mathcal {A}\) has access to a left-or-right oracle, which, given those two trees, consistently either returns a redacted signature for the left pair \((b=0)\) or for the right pair \((b=1)\). The scheme offers privacy if no PPT adversary can decide the origination of received subtree-signature with a non-negligible advantage over \(\frac{1}{2}\).
Definition 7
\(\mathbf {(Privacy).}\) An \(\textsf {RSS}\hbox {-}\textsf {TFRC}:=(\mathsf{KeyGen, Sign, Verify, Redact})\) satisfies privacy preserving requirement if for any PPT adversary \(\mathcal {A}\), the advantage in wining the following game is a negligible function of the security parameter \(\lambda \).
\(\mathbf {Game\,2:}\) Privacy \(_{\mathcal {A}}^{\textsf {RSS}\hbox {-}\textsf {TFRC}}\)
-
Setup: The challenger runs \((pk, sk) \leftarrow \mathsf{KeyGen}(1^{\lambda })\) and sends pk to \(\mathcal {A}\).
-
Phase 1: The adversary \(\mathcal {A}\) can adaptively conduct a polynomially bounded number of queries to the signing oracle. Let \(\varUpsilon _1, \varUpsilon _2, \cdots , \varUpsilon _{Q_1}\) denote the \(Q_1\) quires to signing oracle from \(\mathcal {A}\). For each query, the challenger runs \((\varUpsilon _i, \sigma _{\varUpsilon _i}) \leftarrow \textsf {Sign}(sk, \varUpsilon _i, \mathcal {P}_i)\) and forwards \((\varUpsilon _i, \sigma _{\varUpsilon _i})\) to \(\mathcal {A}\). Note that \(\mathcal {A}\) is also allowed to choose \(\mathcal {P}_i\).
-
Challenge:
-
1.
At the end of Phase 1, adversary \(\mathcal {A}\) finds two identical tree \(\varUpsilon _0\) and \(\varUpsilon _1\) besides the difference of redaction subtrees, i.e., \(\varUpsilon _0\backslash \varUpsilon _{\delta '_0} = \varUpsilon _1 \backslash \varUpsilon _{\delta '_1}\) with \(\varUpsilon _{\delta '_0} \ne \varUpsilon _{\delta '_1}\). Then, adversary \(\mathcal {A}\) sends \((\varUpsilon _0, \varUpsilon _{\delta '_0})\) and \((\varUpsilon _1, \varUpsilon _{\delta '_1})\) to challenger. Note that \(\mathcal {A}\) is also allowed to choose \(\mathcal {P}_0\) and \(\mathcal {P}_1\) such that \(\varUpsilon _0\backslash \varUpsilon _{\delta '_0}\) and \(\varUpsilon _1 \backslash \varUpsilon _{\delta '_1}\) satisfy \(\mathcal {P}_0\) and \(\mathcal {P}_1\), respectively.
-
2.
The challenger chooses \(\varUpsilon _b\) randomly by choosing a bit \(b \in \{0,1\}\) and computes a redactable signature through \((\varUpsilon _b, \sigma _{\varUpsilon _b}) \leftarrow \textsf {Sign}(sk, \varUpsilon _b, \mathcal {P}_b)\) and \((\varUpsilon _{\delta _b}, \sigma _{\varUpsilon _{\delta _b}}) \leftarrow \textsf {Redact}(pk, \varUpsilon _b, \sigma _{\varUpsilon _b}, \varUpsilon _{\delta '_b})\), where \(\varUpsilon _{\delta _b}\) satisfies \(\mathcal {P}_b\). Then the challenger outputs \((\varUpsilon _{\delta _b}, \sigma _{\varUpsilon _{\delta _b}})\).
-
1.
-
Phase 2: In this phase, the adversary \(\mathcal {A}\) can proceed again for polynomially bounded number of queries to the signing oracle adaptively in the same way as Phase 1.
-
Guess: Finally, a guess \(b'\) of b is exported by \(\mathcal {A}\). The adversary wins the above game if \(b' = b\).
The \(\mathrm {Adv_{\mathcal {A}}^\mathsf{Privacy}} (\lambda )= \Big | \mathrm {Pr}[b'=b] - \frac{1}{2} \Big |\) is defined as the advantage that \(\mathcal {A}\) has in the above game. The privacy of RSS-TFRC requires that \(\mathrm {Adv_{\mathcal {A}}^\mathsf{Privacy}} (\lambda )\) is a negligible function of the security parameter \(\lambda \), such that \(\mathrm {Adv_{\mathcal {A}}^\mathsf{Privacy}} (\lambda ) \le \epsilon (\lambda )\).
3.5 Transparency of RSS-TFRC
The above notion of privacy only hides the contents of the deleted nodes, but not necessarily that redaction operation. Transparency is a stronger notion of leakage prevention. It requires that no end-user should be able to infer whether the received tree has been redacted or not. Intuitively, no adversary is able to decide if the given tree-signature pair directly comes from Sign algorithm or Redact algorithm. Let \((\varUpsilon _\delta , \sigma _{\varUpsilon _\delta }) \leftarrow \textsf {Redact}(pk, \varUpsilon , \sigma _\varUpsilon , \varUpsilon _{\delta '})\) be a tree-signature pair derived from \((\varUpsilon , \sigma _\varUpsilon )\) by the application of Redact algorithm, and let \((\varUpsilon _\delta , \sigma _{\varUpsilon _S}) \leftarrow \textsf {Sign}(sk, \varUpsilon _\delta , \mathcal {P})\) be a tree-signature pair generated from scratch. The task for the adversary is to distinguish both cases.
Definition 8
\(\mathbf {(Transparency).}\) An \(\textsf {RSS}\hbox {-}\textsf {TFRC}:=(\mathsf{KeyGen,}\ \mathsf{Sign,}\ \mathsf{Verify,}\ \mathsf{Redact})\) is transparent if for any PPT adversary \(\mathcal {A}\) the advantage in wining the following game is a negligible function of the security parameter \(\lambda \).
\(\mathbf {Game\,3:}\) Transparency \(_{\mathcal {A}}^{\textsf {RSS}\hbox {-}\textsf {TFRC}}\)
-
Setup: The challenger runs \((pk, sk) \leftarrow \mathsf{KeyGen}(1^{\lambda })\) and sends pk to \(\mathcal {A}\).
-
Phase 1: The adversary \(\mathcal {A}\) can adaptively conduct a polynomially bounded number of queries to the signing oracle. Let \(\varUpsilon _1, \varUpsilon _2, \cdots , \varUpsilon _{Q_2}\) denote the \(Q_2\) quires to signing oracle from \(\mathcal {A}\). For each query, the challenger runs \((\varUpsilon _i, \sigma _{\varUpsilon _i}) \leftarrow \textsf {Sign}(sk, \varUpsilon _i, \mathcal {P}_i)\) and forwards \((\varUpsilon _i, \sigma _{\varUpsilon _i})\) to \(\mathcal {A}\). Note that \(\mathcal {A}\) is also allowed to choose \(\mathcal {P}_i\).
-
Challenge:
-
1.
At the end of Phase 1, adversary \(\mathcal {A}\) outputs two trees \(\varUpsilon _0\) and \(\varUpsilon _1\) such that \(\varUpsilon _0 \subseteq \varUpsilon _1\), and a fine-grained redaction control policy \(\mathcal {P}\), where \(\mathcal {P}(\varUpsilon _0)=1\). Then, \(\mathcal {A}\) sends them to the challenger.
-
2.
The challenger randomly chooses a bit \(b \in \{0,1\}\) and computes signature through algorithm \((\varUpsilon _b, \sigma _{\varUpsilon _b}) \leftarrow \textsf {Sign}(sk, \varUpsilon _b, \mathcal {P})\). If \(b=1\), then the signature for \(\varUpsilon _0\) is computed from \(\sigma _{\varUpsilon _1}\): \((\varUpsilon _0, \sigma _{\varUpsilon _0}) \leftarrow \textsf {Redact}(pk, \varUpsilon _1, \sigma _{\varUpsilon _1}, \varUpsilon _1 \backslash \varUpsilon _0)\). Then the challenge \((\varUpsilon _0, \sigma _{\varUpsilon _0})\) is given to \(\mathcal {A}\).
-
1.
-
Phase 2: In this phase, the adversary \(\mathcal {A}\) can continuously have access to the signing, redaction, and verification oracles for polynomially bounded number of queries in the same way as Phase 1.
-
Guess: Finally, a guess \(b'\) of b is exported by \(\mathcal {A}\). The adversary wins the game if \(b' = b\).
The \(\mathrm {Adv_{\mathcal {A}}^\mathsf{Transparency}} (\lambda )= \Big | \mathrm {Pr}[b'=b] - \frac{1}{2} \Big | \) is defined as the advantage that \(\mathcal {A}\) has in the above game. The transparency of RSS-TFRC requires \(\mathrm {Adv_{\mathcal {A}}^\mathsf{Transparency}} (\lambda )\) is a negligible function of the security parameter \(\lambda \), such that \(\mathrm {Adv_{\mathcal {A}}^\mathsf{Transparency}} (\lambda ) \le \epsilon (\lambda )\).
An RSS-TFRC is secure if no PPT adversary \(\mathcal {A}\) can win at least one of the above games with non-negligible advantage.
4 Our Construction
In this section, we propose a construction of efficient RSS-TFRC to support the secure dissemination of authenticated tree-structured data in ODB mode. Our scheme utilizes secure BGLS [2], MSP, LSSS [1] and secure naming scheme [13] as construction primitives. Before outsourcing tree-structured data to DSP, the data owner generates a redactable signature for the data and uploads them to DSP. Once a querier forwards a query to DSP to access parts of the authenticated tree, the DSP executes redaction algorithm and outputs a subtree and its corresponding signature. It should be noticed that the DSP can only generate valid signatures for those subtrees that satisfying the fine-grained redaction control policy defined by the data owner. After receiving the subtree and corresponding signature, the querier can verify the integrity and authenticity of this subtree with the redacted signature and data owner’s public key without obtaining any information about the pruned nodes. The concrete construction of this scheme consists of four algorithms: KeyGen, Sign, Verify and Redact.
\(\textsf {KeyGen}(1^{\lambda })\): This algorithm is identical to the key generation algorithm in BGLS [2]. A signer picks a random \(k \overset{R}{\leftarrow } \mathbb {Z}_p\) and computes \(v \leftarrow g_2^k\). The signer’s public key pk is \( v \in G_2\) and secret key sk is \(k \in \mathbb {Z}_p\).
\(\textsf {Sign}(sk, \varUpsilon (V,E), \mathcal {P})\): This algorithm takes as input a signing secret key sk, a tree \(\varUpsilon (V,E)\) with n nodes, and a fine-grained redaction control policy \(\mathcal {P}\). \(\mathcal {P}\) is built upon the monotone span program and linear secret sharing scheme [24] which allows the signer to control what subtrees a third party can distribute. The policy \(\mathcal {P}\) is depicted by the monotone boolean formula, where the inputs of this formula are associated with the nodes of \(\varUpsilon (V,E)\). This policy can be converted into a monotone span program which is a \(n \times t\) matrix \(\mathbf {M}\). Then, the signer chooses a secret \(s \overset{R}{\leftarrow } \mathbb {Z}_p\) and constructs a vector \(\mathbf {\omega } = (s, y_{2}, \ldots , y_{t})^{T}\) in which \(y_i \overset{R}{\leftarrow } \mathbb {Z}_{p}\) and s is the secret to be divided into n shares. For \(1 \le i \le n\), it calculates \(s_{i} = \mathbf {M} \cdot \mathbf {\omega }\), and each share “belongs" to \(\rho (i)\), where \(\rho \) defines each row number i of matrix \(\mathbf {M}\) as \(\rho (i)\) that labels the rows of \(\mathbf {M}\) with nodes in \(\varUpsilon \). After the construction of fine-grained redaction control policy, signer performs the following steps:
-
1.
Let \(\theta _{x_i}\overset{R}{\leftarrow } \mathbb {Z}_p\) and \(\theta _{p_{x_i}}\overset{R}{\leftarrow } \mathbb {Z}_p\) be the secure names of node \(x_i\) and its parent that are generated through the secure naming scheme in [13].
-
2.
Generate an identity \(id\overset{R}{\leftarrow } \mathbb {Z}_p\) for tree \(\varUpsilon (V,E)\), and let \(m_{x_i}\) be the content of node \(x_i\) in tree \(\varUpsilon (V,E)\).
-
3.
For all \(i~(1 \le i \le n)\) such that node \(x_i \in V\), compute \(h_i \leftarrow h(id \Vert \theta _{p_{x_i}} \Vert \theta _{x_i} \Vert m_{x_i})\) and \(\sigma _i \leftarrow h_i^k\), where \(h: \{0,1\}^*\rightarrow G_1\) is a full-domain hash function.
-
4.
Compute \(\sigma _0 \leftarrow (g_1^s)^k\) and \(z_i \leftarrow g_1^{s_i}\).
-
5.
Compute \(\sigma \leftarrow \prod ^n_{i=0}{\sigma _i}\) and \(\sigma _S \leftarrow e(\sigma , g_2)\). Note that \(\sigma \) is the aggregate signature for \(\sigma _0, \ldots , \sigma _n\).
-
6.
Output \((\varUpsilon (V,E), \sigma _\varUpsilon )\), where \(\sigma _\varUpsilon = (\sigma _S, id, \{z_i\}_{x_i \in V}, \{(\theta _{x_i}, \theta _{p_{x_i}}) | x_i \in V \})\).
\(\textsf {Verify}(pk, \varUpsilon (V,E), \sigma _\varUpsilon )\): This algorithm takes as input a public key pk, a tree \(\varUpsilon \), and a signature \(\sigma _\varUpsilon \). It performs the following steps:
-
1.
For each node \(x_i \in V\), compute \(h_i \leftarrow h(id \Vert \theta _{p_{x_i}} \Vert \theta _{x_i} \Vert m_{x_i})\).
-
2.
Suppose that \(\varUpsilon (V,E)\) satisfies the access structure and let \(I \subset \{1,2,\ldots , n\}\) be defined as \(I=\{i: x_i \in V\}\). Then, there exist constants \(\{\omega _i \in \mathbb {Z}_p\}_{i\in I}\) such that if \(\varUpsilon (V,E)\) is a tree satisfying the fine-grained redaction policy then \(s = \sum _{i \in I} \omega _{i}s_i\).
-
3.
The verifier ensures \(\sigma _S = \prod _{x_i \in V} e(h_i\cdot {z_i}^{\omega _i}, v)\) holds and rejects otherwise.
\(\textsf {Redact}(pk, \varUpsilon _{\delta '}(V_{\delta '},E_{\delta '}), \varUpsilon (V, E), \sigma _\varUpsilon )\): This algorithm takes as input the public key pk of a signer, a subtree \(\varUpsilon _{\delta '}(V_{\delta '},E_{\delta '})\) to be cut, a tree \(\varUpsilon (V, E)\), and a signature \(\sigma _\varUpsilon \). To redact a subtree \(\varUpsilon _{\delta '}(V_{\delta '},E_{\delta '})\), the database service provider executes the redacting operation in the following steps:
-
1.
Check the validity of \((\varUpsilon (V, E), \sigma _\varUpsilon )\) with \(\textsf {Verify}\) algorithm. If the signature is not valid, return \(\bot \).
-
2.
If \(\varUpsilon _{\delta '}(V_{\delta '},E_{\delta '}) \nsubseteq \varUpsilon (V, E)\), return \(\bot \).
-
3.
Cut the subtree \(\varUpsilon _{\delta '}(V_{\delta '},E_{\delta '})\) from \(\varUpsilon (V, E)\), the redacted tree is \(\varUpsilon _{\delta }(V_{\delta },E_{\delta })\).
-
4.
Compute \(\sigma _F \leftarrow \sigma _S/ \prod _{x_i \in V_{\delta '}} e(h_i, v)\) and remove the elements \(\{z_i\}_{x_i \in V_{\delta '}}\) and \(\{(\theta _{x_i}, \theta _{p_{x_i}}) | x_i \in V_{\delta '} \}\) from \(\sigma _\varUpsilon \).
-
5.
Output \((\varUpsilon _{\delta }(V_{\delta },E_{\delta }), \sigma _{\varUpsilon _{\delta }})\), where \(\sigma _{\varUpsilon _{\delta }} = (\sigma _F, id, \{z_i\}_{x_i \in V_{\delta }}, \{(\theta _{x_i}, \theta _{p_{x_i}}) | x_i \in V_{\delta } \})\) and \(V_{\delta } = V \backslash V_{\delta '}\).
The signing correctness of RSS-TFRC is as follows: \(\sigma _S = e(\sigma , g_2) = e(\prod _{i \in I}h_i^k \cdot (g_1^s)^k, g_2) = \prod _{i \in I} e(h_i, v)\cdot e(g_1^s, v) = \prod _{i \in I} e(h_i, v)\cdot e(g_1^{\sum _{i \in I} \omega _{i}s_i}, v) = \prod _{i \in I} e(h_i, v)\cdot e(\prod _{i \in I} g_1^{\omega _{i}{s_i}}, v) = \prod _{i \in I} e(h_i, v)\cdot \prod _{i \in I} e({z_i}^{\omega _i}, v) = \prod _{i \in I} e(h_i \cdot {z_i}^{\omega _i}, v)\).
The redaction correctness of RSS-TFRC is as follows: \(\sigma _F = \sigma _S/ \prod _{i \in L'} e(h_i, v) = \frac{e(\sigma , g_2)}{\prod _{i \in L'} e(h_i, v)} = \frac{e(\prod _{i \in I}h_i^k \cdot (g_1^s)^k, g_2)}{\prod _{i \in L'} e(h_i, v)} = \frac{\prod _{i \in I}e(h_i, v) \cdot e(g_1^s, v)}{\prod _{i \in L'} e(h_i, v)} = \prod _{i \in L}e(h_i, v) \cdot e(g_1^{\sum _{i \in L} \omega _{i}s_i}, v) = \prod _{i \in L}e(h_i, v) \cdot \prod _{i \in L} e({z_i}^{\omega _i}, v) = \prod _{i \in L}e(h_i \cdot {z_i}^{\omega _i}, v)\), where \(L \subset \{1,2,\ldots , n\}\) is defined as \(L =\{i: x_i \in V_{\delta }\}\) and \(L' \subset \{1,2,\ldots , n\}\) is defined as \(L' =\{i: x_i \in V_{\delta '}\}\).
5 Analysis of Our Proposed Scheme
5.1 Security Analysis
In this subsection, we prove the security of our proposed scheme in the aspects of unforgeability, privacy, and transparency. It has been proved that transparency is a stronger notion than privacy [4], which implies privacy. Hence, we only prove the transparency of our scheme. The unforgeability and transparency proofs of our scheme are presented as follows.
Unforgeability of Our Proposed Scheme
Definition 9
A forger \(\mathcal {A}(t, q_S, q_H, \epsilon )\)-breaks a signature scheme if \(\mathcal {A}\) runs in time at most t, \(\mathcal {A}\) makes at most \(q_S\) signature queries and at most \(q_H\) queries to the hash function, and the probability that \(\mathcal {A}\) wins in the above game is at least \(\epsilon \), taken over the coin tosses of \(\mathsf{KeyGen}\) and of \(\mathcal {A}\). A signature scheme is \((t, q_S, q_H, \epsilon )\)-existentially unforgeable under an adaptive chosen-tree attack if no forger \((t, q_S, q_H, \epsilon )\)-breaks it.
Theorem 1
The proposed scheme is unforgeable, as defined in Definition 6.
The proof of Theorem 1 is detailed in Appendix A.
Transparency of Our Proposed Scheme
Theorem 2
Our construction is transparent in the information-theoretical sense, as defined in Definition 8.
Proof
Our scheme is also transparent in the information-theoretical sense. In another word, the secret bit b is perfectly hidden. Our signing algorithm requires that s is always fresh and chosen uniformly, which results in a uniformly distributed aggregate signature. Removing a random number of individual signatures from the aggregate signature also leads to a uniformly distributed signature again. Hence, even an unbounded adversary is not able to guess the bit better than at random. For the redacted message, if the redacted message would have been signed directly, the distributions are still uniform and it is impossible for any adversary to guess b better than at random. Besides, no information about removed nodes of the originally signed tree remains in the redacted signature. Thus our scheme is transparent in an information theoretic sense. \({} \Box \)
5.2 Performance Analysis
In this subsection, we analyze the efficiency of our scheme and make a comparison in terms of computation, communication cost and functionality with several existing RSSs for trees [4, 14, 18, 22]. The purpose of the comparison is to show that our RSS-TFRC achieves a much more flexible functionality of redaction control without compromising on enormous computation or communication cost.
Theoretical Analysis. We first analyze the efficiency of our proposed scheme from a theoretical view. Table 1 presents the comparison between our scheme and four existing RSSs for trees [4, 14, 18, 22]. As we can see, our scheme is the only one to achieve fine-grained redaction control (FRC) without sacrificing performance obviously, and fully supports non-leaves redaction (NLR) and structural integrity (SI) verification. As for the computation cost, our scheme has slightly higher cost in the signature generation (\(\sigma _\varUpsilon \)) than [14, 18] but indistinct cost compared with [4, 22]. Since it requires one bilinear pairing computation for each node, our scheme has a slightly higher cost in verification than others. Moreover, since our scheme adopted BGLS scheme, it saves substantial communication cost than others. Thus, our scheme is more desirable for ODB model according to the above analysis.
Experimental Analysis. Note that in order to precisely measure the performance of our scheme, we further conduct a thorough experimental evaluation of our scheme. All the experiments are implemented by utilizing the PBC library (version 0.5.14) and GMP library (version 6.1.2). The tests platform is set to be: Intel T8300 Dual Core @2.40 GHz and 4 GiB of RAM, 500 G/5400 rpm hard disk. The OS was Ubuntu 10.10 LTS (64 Bit) with Java version 1.6.0_26-b03. We take the median value of 10 runs for each test result. We evaluate three sizes of curves, i.e. 128 and 256 Bit. Since the scheme proposed in [22] is also based on the bilinear aggregate signature [2], we make a comparison with their experiment result. Table 2 presents the running time of signing algorithm, redaction algorithm, and verification algorithm for trees with 10, 50 and 100 nodes. As shown in Table 2, the signature generation process takes longer time than other two algorithms, and this increases dramatically when the number of nodes changes from 10 to 50 and the size of curves changes from 128 bits to 256 bits. However, redaction operation is negligible in terms of the performance for large trees. Although our scheme is not as efficient as [22], it remains within usable limits. This is because the advanced features of our scheme come at a price: we realize fine-grained redaction control in RSSs for trees which slows the runtime of each algorithm.
In summary, through the performance analysis, we can see that our RSS-TFRC achieves fine-grained redaction control and privacy preservation in authenticated tree-structured data dissemination without introducing a great amount of additional complexity.
6 Conclusion
In this paper, we explored the problem of the integrity and origin verification of disseminated tree-structured data with privacy protection and dissemination control in ODB model. To address this problem, we proposed an efficient RSS-TFRC which allows DSP to disseminate partial of authenticated tree-structured data with privacy protection in ODB model. The proposed scheme simultaneously supports the integrity and origin verifications of queried results without disclosing any privacy of data owners, and prevents the dishonest DSP or attackers from returning fake records to the users. Based on the thorough security analysis, we proved the RSS-TFRC is secure against the security threats of signature forgery, privacy disclosure, and information leakage. Finally, the theoretical analysis and experimental results demonstrate that our approach is indeed an efficient and practical solution for the fine-grained dissemination of authenticated trees with privacy protection in ODB model.
It is also important to consider how to design a sort of RSSs for multimedia data sharing, which allow certain types of image modification (e.g. lossy compression and redaction). This kind of RSSs can solve the authenticity and privacy leakage problems in multimedia data sharing. In order to realize the redaction function, signature length of most RSSs has a linear relationship with the number of sub-message blocks, which is impractical in some scenarios with limited communication resources. Therefore, it is urgent to design RSSs with constant signature length by applying aggregate signature schemes, accumulators etc. We hope that our future work will consider the above issues and develop more practical and functional RSSs to satisfy the security requirements in different scenarios.
References
Beimel, A.: Secure schemes for secret sharing and key distribution. Ph.D. thesis, Israel Institute of Technology, Technion, Haifa, Israel (1996)
Boneh, D., Gentry, C., Lynn, B., Shacham, H.: Aggregate and verifiably encrypted signatures from bilinear maps. In: Biham, E. (ed.) EUROCRYPT 2003. LNCS, vol. 2656, pp. 416–432. Springer, Heidelberg (2003). https://doi.org/10.1007/3-540-39200-9_26
Boneh, D., Lynn, B., Shacham, H.: Short signatures from the weil pairing. In: Boyd, C. (ed.) ASIACRYPT 2001. LNCS, vol. 2248, pp. 514–532. Springer, Heidelberg (2001). https://doi.org/10.1007/3-540-45682-1_30
Brzuska, C., et al.: Redactable signatures for tree-structured data: definitions and constructions. In: Zhou, J., Yung, M. (eds.) ACNS 2010. LNCS, vol. 6123, pp. 87–104. Springer, Heidelberg (2010). https://doi.org/10.1007/978-3-642-13708-2_6
Bull, L., Squire, D.M.G., Zheng, Y.: A hierarchical extraction policy for content extraction signatures. Int. J. Digit. Libr. 4(3), 208–222 (2004)
Fu, Z., Ren, K., Shu, J., Sun, X., Huang, F.: Enabling personalized search over encrypted outsourced data with efficiency improvement. IEEE Trans. Parallel Distrib. Syst. 27(9), 2546–2559 (2016)
Goyal, V., Pandey, O., Sahai, A., Waters, B.: Attribute-based encryption for fine-grained access control of encrypted data. In: Proceedings of the 13th ACM Conference on Computer and Communications Security, pp. 89–98. ACM (2006)
Hacigumus, H., Iyer, B., Mehrotra, S.: Providing database as a service. In: 2002 Proceedings of 18th International Conference on Data Engineering, pp. 29–38. IEEE (2002)
Jain, R., Prabhakar, S.: Trustworthy data from untrusted databases. In: 2013 IEEE 29th International Conference on Data Engineering (ICDE), pp. 529–540. IEEE (2013)
Johnson, R., Molnar, D., Song, D., Wagner, D.: Homomorphic signature schemes. In: Preneel, B. (ed.) CT-RSA 2002. LNCS, vol. 2271, pp. 244–262. Springer, Heidelberg (2002). https://doi.org/10.1007/3-540-45760-7_17
Karchmer, M., Wigderson, A.: On span programs. In: Proceedings of 1993 Eighth Annual Conference on Structure in Complexity Theory, pp. 102–111. IEEE (1993)
Kundu, A., Atallah, M.J., Bertino, E.: Efficient leakage-free authentication of trees, graphs and forests. IACR Cryptology ePrint Archive, vol. 2012, p. 36 (2012)
Kundu, A., Atallah, M.J., Bertino, E.: Leakage-free redactable signatures. In: Proceedings of the Second ACM Conference on Data and Application Security and Privacy, pp. 307–316. ACM (2012)
Kundu, A., Bertino, E.: Structural signatures for tree data structures. Proc. VLDB Endow. 1(1), 138–150 (2008)
Liu, J., Huang, X., Liu, J.K.: Secure sharing of personal health records in cloud computing: ciphertext-policy attribute-based signcryption. Future Gener. Comput. Syst. 52, 67–76 (2015)
Ma, J., Liu, J., Huang, X., Xiang, Y., Wu, W.: Authenticated data redaction with fine-grained control. IEEE Trans. Emerg. Top. Comput. (2017)
Ma, J., Liu, J., Wang, M., Wu, W.: An efficient and secure design of redactable signature scheme with redaction condition control. In: Au, M.H.A., Castiglione, A., Choo, K.-K.R., Palmieri, F., Li, K.-C. (eds.) GPC 2017. LNCS, vol. 10232, pp. 38–52. Springer, Cham (2017). https://doi.org/10.1007/978-3-319-57186-7_4
de Meer, H., Pöhls, H.C., Posegga, J., Samelin, K.: Redactable signature schemes for trees with signer-controlled non-leaf-redactions. In: Obaidat, M.S., Filipe, J. (eds.) ICETE 2012. CCIS, vol. 455, pp. 155–171. Springer, Heidelberg (2014). https://doi.org/10.1007/978-3-662-44791-8_10
Merkle, R.C.: A certified digital signature. In: Brassard, G. (ed.) CRYPTO 1989. LNCS, vol. 435, pp. 218–238. Springer, New York (1990). https://doi.org/10.1007/0-387-34805-0_21
Miyazaki, K., Hanaoka, G., Imai, H.: Digitally signed document sanitizing scheme based on bilinear maps. In: Proceedings of the 2006 ACM Symposium on Information, Computer and Communications Security, pp. 343–354. ACM (2006)
Miyazaki, K., Iwamura, M., Matsumoto, T., Sasaki, R., Yoshiura, H., Tezuka, S.: Digitally signed document sanitizing scheme with disclosure condition control. IEICE Trans. Fundam. Electron. Commun. Comput. Sci. 88(1), 239–246 (2005)
Samelin, K., Pöhls, H.C., Bilzhause, A., Posegga, J., de Meer, H.: Redactable signatures for independent removal of structure and content. In: Ryan, M.D., Smyth, B., Wang, G. (eds.) ISPEC 2012. LNCS, vol. 7232, pp. 17–33. Springer, Heidelberg (2012). https://doi.org/10.1007/978-3-642-29101-2_2
Samelin, K., Pöhls, H.C., Bilzhause, A., Posegga, J., de Meer, H.: On structural signatures for tree data structures. In: Bao, F., Samarati, P., Zhou, J. (eds.) ACNS 2012. LNCS, vol. 7341, pp. 171–187. Springer, Heidelberg (2012). https://doi.org/10.1007/978-3-642-31284-7_11
Shamir, A.: How to share a secret. Commun. ACM 22(11), 612–613 (1979)
Steinfeld, R., Bull, L., Zheng, Y.: Content extraction signatures. In: Kim, K. (ed.) ICISC 2001. LNCS, vol. 2288, pp. 285–304. Springer, Heidelberg (2002). https://doi.org/10.1007/3-540-45861-1_22
Wang, Q., Wang, C., Ren, K., Lou, W., Li, J.: Enabling public auditability and data dynamics for storage security in cloud computing. IEEE Trans. Parallel Distrib. Syst. 22(5), 847–859 (2011)
Wu, Z.Y., Hsueh, C.W., Tsai, C.Y., Lai, F., Lee, H.C., Chung, Y.: Redactable signatures for signed CDA documents. J. Med. Syst. 36(3), 1795–1808 (2012)
Xia, Z., Wang, X., Sun, X., Wang, Q.: A secure and dynamic multi-keyword ranked search scheme over encrypted cloud data. IEEE Trans. Parallel Distrib. Syst. 27(2), 340–352 (2016)
Acknowledgment
We thank several anonymous reviewers for their excellent feedback. This work is supported by National Natural Science Foundation of China (61472083, 61771140) and Distinguished Young Scholars Fund of Fujian (2016J06013).
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Appendix A Proof for Theorem 1
Appendix A Proof for Theorem 1
We will show that if either of the following attackers can succeed in forging a signature for a tree with nonnegligible probability, then we can construct an algorithm \(\mathcal {B}\) to solve the co-CDH problem on \((G_1, G_2)\) with nonnegligible probability in the similar method as [3, 20].
-
There exists an attacker \(\mathcal {A}_f\) who generates a valid signature for a tree consisting subtrees of a tree that has never been queried to signing oracle, or
-
an attacker \(\mathcal {A}_a\) who produces a valid signature for a tree that is a subtree of a tree that has been queried to signing oracle but does not satisfy the redaction control policy.
Attacker 1. Firstly, we will show how to construct a \(t'\)-time algorithm \(\mathcal {B}_f\) that solves co-CDH problem on \((G_1, G_2)\) with probability at least \(\epsilon '\) by using the attacker \(\mathcal {A}_f\). This will contradict the fact that \((G_1, G_2)\) is a \((t', \epsilon ')\)-co-CDH group pair.
Proof
Let \(g_2\) be a generator of \(G_2\). Algorithm \(\mathcal {B}_f\) is given \(g_2, u \in G_2\) and \(h \in G_1\), where \(u=g_2^a\). Its goal is to output \(h^a \in G_1\). Algorithm \(\mathcal {B}_f\) simulates the challenger and interacts with forger \(\mathcal {A}_f\) as follows.
Setup. Algorithm \(\mathcal {B}_f\) starts by giving \(\mathcal {A}_f\) the generator \(g_2\) and the public key \(v' = u \cdot g_2^r \in G_2\), where r is a random in \(\mathbb {Z}_p\).
Hash Queries. At any time algorithm \(\mathcal {A}_f\) can query the random oracle H. To respond to these queries, \(\mathcal {B}_f\) maintains a list of tuples \(\langle M_j, w_j, b_j, c_j \rangle \) as explained below. We refer to this list as the H-list which is initially empty. When \(\mathcal {A}_f\) queries the oracle H at a point \(M_i \in \{0,1\}^*\), \(\mathcal {B}_f\) responds as follows:
-
1.
If the query \(M_i\) already appears on the H-list in a tuple \(\langle M_i, w_i, b_i, c_i\rangle \) then algorithm \(\mathcal {B}_f\) responds with \(H(M_i)=w_i \in G_1\).
-
2.
Otherwise, \(\mathcal {B}_f\) generates a random coin \(c_i \in \{0,1\}\) so that \(\mathrm {Pr}[c_i=0]=1-1 / (nq_{S} + n)\).
-
3.
Algorithm \(\mathcal {B}_f\) picks a random \(b_i \in \mathbb {Z}_p\) and computes \(w_i \leftarrow h^{c_i}\cdot \psi (g_2)^{b_i} \in G_1\).
-
4.
Algorithm \(\mathcal {B}_f\) adds the tuple \(\langle M_i, w_i, b_i, c_i\rangle \) to the H-list and responds to \(\mathcal {A}_f\) by setting \(H(M_i)=w_i\).
Note that, either way, \(w_i\) is uniformly distributed in \(G_1\) and is independent of \(\mathcal {A}_f\)’s current view as required.
Signature Queries. Let a tree \(\varUpsilon (V, E)\) with distribution control policy \(\mathcal {P}\) be a signing query issued by \(\mathcal {A}_f\) under the challenge public key \(v'\). Algorithm \(\mathcal {B}_f\) responds this query as follows:
-
1.
Algorithm \(\mathcal {B}_f\) generates secure names \(\theta _{x_i}\) and \(\theta _{p_{x_i}}\) for node \(x_i\) and its parent in tree \(\varUpsilon (V, E)\) and an identity id for \(\varUpsilon (V, E)\) the same way as in step 1 and step 2 of the signing algorithm of the proposed scheme, respectively.
-
2.
Algorithm \(\mathcal {B}_f\) runs the above algorithm for responding to H-queries to obtain a \(w_i \in G_1\) such that \(H(M_i)=w_i\). Without loss of generality we can assume \(\langle M_i, w_i, b_i, c_i\rangle \) to be the tuple on the H-list corresponding to each node \(x_i\).
-
3.
If \(c_i =1\) for all \(x_i \in V\), then \(w_i =\psi (g_2)^{b_i} \in G_1\). Algorithm \(\mathcal {B}_f\) defines \(\sigma _i = \psi (u)^{b_i} \cdot \psi (g_2)^{rb_i}\). Observe that \(\sigma _i = {w_i}^{a+r}\) and therefore \(\sigma _i\) is a valid signature on \(M_i\) under the public key \(u \cdot g_2^r = g_2^{a+r}\). If \(c_i =0\) then \(\mathcal {B}_f\) reports failure and terminates.
-
4.
Algorithm \(\mathcal {B}_f\) picks a random \(s \in \mathbb {Z}_p\) and computes \(w_0 \leftarrow h^{c_0} \cdot \psi (g_2)^s \in G_1\). Algorithm \(\mathcal {B}_f\) defines \(\sigma _0 = \psi (u)^s \cdot \psi (g_2)^{rs}\). Algorithm \(\mathcal {B}_f\) defines \(z_i = \psi (g_2)^{s_i}\) the same way as the signing algorithm of the proposed scheme. Observe that \(\sigma _0 = w_0^{a+r}\) and therefore \(\sigma _0\) is a valid signature on \(w_0\) under the public key \(u \cdot g_2^r = g_2^{a+r}\). Then, algorithm \(\mathcal {B}_f\) computes \(\sigma \leftarrow \prod ^n_{i=0}{\sigma _i}\). Algorithm \(\mathcal {B}_f\) computes \(\sigma _S = e(\sigma , g_2)\) and gives \(\sigma _\varUpsilon \) to \(\mathcal {A}_f\), where \(\sigma _\varUpsilon = (\sigma _S, id, \{z_i\}_{x_i \in V}, \{(\theta _{x_i}, \theta _{p_{x_i}}) | x_i \in V \})\).
Output. Eventually, \(\mathcal {A}_f\) halts. It either concedes failure, in which case so does \(\mathcal {B}_f\), or it returns a forged, but valid signature for a tree \(\varUpsilon ^*\) such that no signature query was issued for even one node of tree \(\varUpsilon ^*\). If there is no tuple on the H-list containing nodes of \(\varUpsilon ^*\) then \(\mathcal {B}_f\) issues a hash query itself for each node of \(\varUpsilon ^*\) to ensure that each node in \(\varUpsilon ^*\) has such a tuple. We assume \(\sigma _{\varUpsilon ^*}\) is a valid signature on \(\varUpsilon ^*\) under the given public key; if it is not, \(\mathcal {B}_f\) reports failure and terminates.
Next, algorithm \(\mathcal {B}_f\) finds a set of tuple \(\{\langle M_i^*, w_i^*, b_i^*, c_i^* \rangle \}_{i \in I}\) on the H-list, where \(I \subset \{1,2,\ldots , n\}\) is defined as \(I =\{i: x_i \in V^*\}\). Algorithm \(\mathcal {B}_f\) now proceeds only if \(c_0^* \ne 0\) and \(c_i^*=0~(1 \le i \le n)\); otherwise \(\mathcal {B}_f\) reports failure and halts. Since \(c_0^* =1\), it follows that \(w_0^* = h \cdot \psi (g_2)^{s^*}\). For \(1 \le i \le n\), since \(c_i^*=0\), it follows that \(w_i^* = \psi (g_2)^{b_i^*}\). The aggregate signature \(\sigma ^*\) in \(\sigma _{\varUpsilon ^*}\) must satisfy verification equation, \(e(\sigma ^*, g_2) = \prod _{x_i \in V} e(w_i^*\cdot {z_i^*}^{\omega _i}, v')\). For each \(i \ge 1\), \(\mathcal {B}_f\) sets individual signature \(\sigma _i^* = \psi (u)^{b_i^*} \cdot \psi (g_2)^{rb_i^*}\). Then \(\mathcal {B}_f\) computes the value \(\sigma _0^*\) as \(\sigma _0^* \leftarrow \sigma ^*/\prod ^n_{i=1} \sigma _i^*\). This is a valid signature for \(w_0^*\) because \(e(\sigma _0^*) = e(\sigma ^*, g_2) \cdot \prod ^n_{i=1} e(\sigma _i^*, g_2)^{-1} = \prod ^n_{i=0} e(w_i^*, v') \cdot \prod ^n_{i=1} e(w_i^*, v')^{-1} = e(w_0^*, v')\). Since \(w_0^* = h \cdot \psi (g_2)^{s^*}\), this implies that \(\sigma _0^* = (h \cdot \psi (g_2)^{s^*})^{a+r}\). Then \(\mathcal {B}_f\) calculates and outputs the required \(h^a\) as \(h^a \leftarrow \sigma _0^*/ (h^r \cdot \psi (u)^{s^*} \cdot \psi (g_2)^{rs^*})\).
This completes the description of algorithm \(\mathcal {B}_f\). It remains to show that \(\mathcal {B}_f\) solves the given instance of the co-CDH problem in \((G_1, G_2)\) with probability at least \(\epsilon '\). To do so, we analyze the three events needs for \(\mathcal {B}_f\) to succeed:
-
\(\varepsilon _1\): \(\mathcal {B}_f\) does not abort as a result of any of \(\mathcal {A}_f\)’s signature queries.
-
\(\varepsilon _2\): \(\mathcal {A}_f\) generates a valid tree-signature forgery \((\varUpsilon ^*, \sigma _{\varUpsilon ^*})\).
-
\(\varepsilon _3\): Event \(\varepsilon _2\) occurs, and in addition, \(c_0^* \ne 0\) and \(c_i^* = 0~(1 \le i \le n)\), where \(c_i^*\) is the c-component of the tuple containing \(M_i^*\) on the H-list.
\(\mathcal {B}_f\) succeeds if all of these events happen. The probability Pr\([\varepsilon _1 \wedge \varepsilon _3]\) is: \(\text{ Pr } [\varepsilon _1 \wedge \varepsilon _3]= \text{ Pr } [\varepsilon _1] \cdot \text{ Pr } [\varepsilon _2 | \varepsilon _1] \cdot \text{ Pr } [\varepsilon _3 | \varepsilon _1 \wedge \varepsilon _2]\).
The probability that algorithm \(\mathcal {B}_f\) does not abort as a result of \(\mathcal {A}_f\)’s signature queries is at least \((1-1/(nq_S+n))^{nq_S}\), since the c-component of the tuple on the H-list is independent of \(\mathcal {A}_f\)’s view. Hence, \(\text{ Pr } [\varepsilon _1] \ge (1-1/(nq_S+n))^{nq_S}\).
If the event \(\varepsilon _1\) happens, all \(\mathcal {A}_f\)’s responses to \(\mathcal {B}_f\)’s signature queries are valid. Since the public key given to \(\mathcal {A}_f\) is from the same distribution as public key produced by \(\textsf {KeyGen}\) algorithm. Responses to hash queries are as in the real attack since each response is uniformly and independently distributed in \(G_1\). Since \(\mathcal {B}_f\) did not abort as a result of \(\mathcal {A}_f\)’s signature queries, all its responses to those queries are valid. Therefore \(\mathcal {B}_f\) will produce a valid signature forgery with probability at least \(\epsilon \). Hence \(\text{ Pr } [\varepsilon _2 | \varepsilon _1] \ge \epsilon \).
If the event \(\varepsilon _1\) and \(\varepsilon _2\) happen, the forged signature satisfies \(c_0^* \ne 0\) and \(c_i^* = 0~(1 \le i \le n)\) with the probability as least \((1-1/(nq_S+n))^{n-1}\,\cdot \,1/(nq_S+n)\), since all \(c_i\)s are independent of one another. Hence, \(\text{ Pr } [\varepsilon _3 | \varepsilon _1 \wedge \varepsilon _2] \ge (1-1/(nq_S+n))^{n-1}\cdot 1/ (nq_S +n)\).
Algorithm \(\mathcal {B}_f\) produces the correct answer with probability at least \(\epsilon ' \geqslant Pr[\varepsilon _1 \wedge \varepsilon _3] \geqslant (1-\frac{1}{nq_S+n})^{(nq_S+n-1)} \cdot \frac{1}{nq_S +n} \cdot \epsilon \geqslant \frac{\epsilon }{e(nq_S+n)}\), where e is the base of natural logarithms.
This indicates that if the forger algorithm \(\mathcal {A}_f\) succeeds in forging a signed tree with nonnegligible probability \(\epsilon \), then an algorithm \(\mathcal {B}_f\) solving the co-CDH problem on \((G_1, G_2)\) with nonnegligible probability \(\epsilon '\) exists. Algorithm \(\mathcal {B}_f\)’s running time is the same as \(\mathcal {A}_f\)’s running time plus the time it takes to respond to hash queries and signature queries. Each query requires an exponentiation in \(G_1\) which we assume takes time \(c_{G_1}\). The output phase requires at most n additional hash computations, two inversions, two exponentiations, and \(n-1\) multiplications. Hence, the total running time is at most \(t+ c_{G_1}(q_H+2q_S+n+4)+n \le t'\) as required. This completes the proof of Theorem 1.
Attacker 2. We will show how to construct a \(t'\)-time algorithm \(\mathcal {B}_a\) that solves co-CDH problem on \((G_1, G_2)\) with probability at least \(\epsilon '\) by using the attacker \(\mathcal {A}_a\). This will contradict the fact that \((G_1, G_2)\) is a \((t', \epsilon ')\)-co-CDH group pair.
The proof process is analogous to Attacker 1. Hence, we omit it for the page limit. \({} \Box \)
Rights and permissions
Copyright information
© 2018 Springer Nature Switzerland AG
About this paper
Cite this paper
Liu, J., Ma, J., Zhou, W., Xiang, Y., Huang, X. (2018). Dissemination of Authenticated Tree-Structured Data with Privacy Protection and Fine-Grained Control in Outsourced Databases. In: Lopez, J., Zhou, J., Soriano, M. (eds) Computer Security. ESORICS 2018. Lecture Notes in Computer Science(), vol 11099. Springer, Cham. https://doi.org/10.1007/978-3-319-98989-1_9
Download citation
DOI: https://doi.org/10.1007/978-3-319-98989-1_9
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-98988-4
Online ISBN: 978-3-319-98989-1
eBook Packages: Computer ScienceComputer Science (R0)